Sunday, December 27, 2009
SmartSwipe (and HomeATM)- A Very Smart Tool For The Cautious Online Shopper
The device is the SmartSwipe by Canadian company NetSecure.
I had a hard time believing that what the catalog was claiming was possible, but then after reading the white-paper on it at the SmartSwipe site I think it's incredibly smart. With this device installed, it's driver is used by the web browser as an encryption engine. The browser (for now it only works with IE) passes off the unencrypted form to the device, which inserts the creditcard data into the form an encrypts the page before passing it back to the browser to transmit to the store website. The device does the encryption, not the browser, so since the card scanning and encryption are done outside the computer, there is no unencrypted data for spyware running on the user's PC to read.
Normally, if you typed it in yourself, there are a number of places where spyware or keyloggers could grab the unencrypted data before the browser gets a chance to encrypt it to pass it securely over the net to the store.
This way the spyware would have to be running on the card reader (which for now anyway, isn't an issue, no one has written spyware that runs in the external card reader) so, it is safe from all the current spyware until it gets to the store's end of the chain.
These are very nice, and I hope that they manage to work deals with the major manufacturers to install these, or better yet, a next generation chip and pin version directly into new PCs.
The SmartSwipe is probably not the only such device out there, the technology to look for if you find another device like it is called Dynamic SSL. I believe Dynamic SSL is the future for secure online shopping.
For a little company from Saskatchewan, they certainly have made inroads with this device being carried by Costco, Futureshop, Dell and Amazon already, and it only works with 32 bit Internet Explorer so far. Once it works with other browsers it'll probably become a commonplace tool for regular internet shoppers.
[Ed note: Only a few hours after the initial post which mentioned only SmartSwipe, a sales person from Home ATM posted a comment. Therefore I have changed the title to reflect that. Having read the website at http://www.homeatm.net I cannot say for sure how the HomeATM works, but I am really disappointed in the video demo that they use to show how secure it is. The fault in the video isn't really with the device itself, but the method that Western Union used to send the money that was taken from his account to the recipient.
Sure, it was securely transferred from his account to Western Union, but then Western Union sent an unencrypted e-mail to a Gmail account with a web link and all the details including a password needed to retrieve the funds. Anyone who could intercept that e-mail could take the money before it got to the recipient. Sure, then it is securely transferred to the hacker's account from Western Union, but the intended recipient is left with nothing.
It is not the device's fault how Western Union chose to implement the transfer, what W.U. should have done was what the Canadian banks on the Interac system do and have the user create a password that they tell the recipient OUT OF BAND so that an intercepted e-mail transfer is still secured by a password that is not known to the intercepting bad guy. It is a poor marketing choice to use a video of a system with such an obvious security problem to demonstrate a security device.
The biggest problem I see with the device itself, aside from being a magstripe and PIN device as opposed to Chip and PIN (which I'm sure will be the next version) is that there doesn't seem to be any way to actually get one.]
Friday, December 18, 2009
New Adobe Reader Vunerability
As usual the fix is to disable JavaScript in Acrobat Reader. Adobe won't have a patch out till Jan 12.
If you have to do it network wide follow the instructions from this post I did back in October to do it via logon scripts.
Upgrade to 9.2 even though it is technically vulnerable, if you turn off JavaScript (which you should do even after the patch is out) 9.2 will let you enable JavaScript on a document by document basis as needed. (usually it is NOT necessary)
Monday, December 14, 2009
Xmas Gifts For Techies 2009
1. PS3 slim. One of the first posts on this blog back in 2006 was the PS3 line watch. Back then I was drooling with anticipation of the upcoming PS3. I bought one in the summer of 2007 because I was stuck at home all day for a few months because of a car accident. ...even back then with hardly any games available it was fun. The new slim version is out now for this Xmas season. It doesn't play PS2 games anymore, and only plays PS1 games if you download them from the online store (about $6 each) but there are lots of PS3 games and bluray movies out now so that's not much of an issue, and if it is, you can always pick up a PS2 slim to go with it for peanuts.
2. Drobo. Every techie needs more disk space... constantly. Drobo will manage it all by itself. You just stick a disk in, when you need more space you stick in another disk, when you need more, stick in another. when you run out of slots to stick disks into you pull out the smallest disk and stick a bigger one in in it's place. No config, no copying files around, it takes care of it all for you.
3. ReadyNAS. For the techie that has more stringent requirements for his/her data storage, ReadyNAS is like Drobo on steroids.
4.Amazon's Kindle e-book reader. For a geek or a book lover (or a geeky book lover) this is a great gift idea. It stores and displays (in black and white) books and magazines bought through Amazon or downloaded as PDF. It has a rechargeable battery, but it only needs to be charged about once a week, even when the wireless is left on all the time. You can go much longer than that if you remember to turn off the wireless connection when you aren't actually downloading a new book.
Network Vulnerability Scanners
One other option that has come up since then is the new much easier to use web-based Nessus 4.2.
Nessus has always been free for home users, but now I feel that it's easy enough for most home users to set up. It comes in a windows version, and there is only the server end to set up now, everything else is done through a browser.
Unfortunately the Pro version of Nessus is a little pricey for the average small business at $1200 per year, but you can hire a pro, like me, to come in and scan your network on a regular basis with this tool for probably a fair bit less than that. (pro licenses are not tied to a physical network, but limited to one machine... so if that machine is a laptop, a pro feed license can go wherever the security contractor takes it.)
Rapid 7 has also recently released NeXpose Community Edition, which I have yet to try out, but is free to use for a network of up to 32 PCs, and there is the open source OpenVAS, which was spun off from Nessus back at version 2, when Nessus was still an open source project. These 2 options I suspect would be more difficult to get up and running than the first two, as they are really aimed at folks with a high level of tech knowledge. NeXpose comes in several other versions for varying levels of additional features, and larger networks, but it is more expensive than the Nessus Pro feed, so very much out of the reach of the average small business or home user, but the Community edition is supposed to be very good, and I'll be playing around with it in the next few weeks and I will let you all know what I think.
No matter which you choose, scanning your network, especially for business networks, is an important part of keeping your network secure. If you don't scan it to find the holes in your security, someone else will, and they probably won't point out the holes to you, they'll probably just use those holes in ways you don't want them to.
One other option, from the folks at Rapid 7 is the free online scan. You can scan 2 IP addresses for free from the internet at http://www.rapid7.com/freescan.jsp This should give you an idea of how exposed your servers that are attached to the internet are. This will only scan public Internet IP addresses. It is probably best to get a local scanner set up or hire a pro to come in and scan the private address space as well, especially if you use wireless.
Friday, December 11, 2009
Making E-mail Private
If you didn't and you use Gmail, go read it now. It only takes about 10 minutes to read and another 10 minutes to implement.
Now, I have to wonder why is it that people never seem to care enough about privacy to encrypt e-mails?
Sure, for some it's a matter of not knowing you CAN encrypt, for others it's a not knowing HOW to do it... but it seems the biggest thing is an aversion to using passwords.
I have a 30 character password that I type in whenever I want to encrypt or digitally sign an e-mail. Most people would not go to such an extreme, but even a 6 or 8 character password with PGP or GnuPG that you only had to type once per mail session, when you first open your mail program or when you send the first message that day, would afford a lot more privacy and ensure that mail you think is from friend X isn't really from stranger Y pretending to be friend X.
How many people have had an e-mail come to them apparently from a friend that turned out to be spam, or worse, a virus? ...or even a roommate playing a practical joke on the supposed sender? PGP/GPG would solve that. I've been using this technology on an off (and recently more and more) for years, but surprisingly few others I know use it. I could understand if it were like S/MIME encryption that requires a yearly fee for a certificate, but PGP is free. All it takes is a little bit of effort to get started then you can stop sending love letters and secret passwords and Grandma's secret family recipes on the electronic equivalent of postcards and start mailing things in e-envelopes. (strong e-envelopes).
If anyone reading this is thinking "hey, I should do that, but it's too hard" e-mail me and I'll help you get started. ...just don't get discouraged if Microsoft and I are the only ones who even send you signed e-mails for a while. It's something that will take time to catch on amongst your friends, and that many people won't ever bother with....some folks will always think that secret codes are only for spies and criminals, but if you don't try to protect your privacy, who will?
Rod MacPherson
rod@macphersonclan.com
My PGP key
Friday, October 23, 2009
Upgrading From An Old BlackBerry?
People still think of PIN as being more private than e-mail, but it is not. It can be, and often is, logged at one or both end's corporate servers, but if your contacts have an old PIN# in their address books and they try to PIN you a message, but somone else owns that Blackberry device now, guess who gets the message!
Wednesday, October 21, 2009
Tips Of The Day
http:
Wednesday, October 14, 2009
Adobe Virus Update
reg add "HKCU\Software\Adobe\Acrobat Reader\9.0\JSPrefs" /v bEnableJS /t REG_DWORD /d 0 /f
Friday, October 09, 2009
More Adobe PDF Viruses On The Loose Patch On The Way
YES you CAN!!! and Seth Hardy of Symantec's MessageLabs just did a talk the other day at SecTor 2009 about how he's been able to (in a test lab) create a virus, embed it in a PDF and get past every known antivirus. This is scary stuff folks, and there is one little thing you can do to stop most of it.
HelpNet Security says that a new round of these viruses is out in the wild and Acrobat 9.1.3 is vulnerable, but a patch is coming on Oct. 13th. In the meantime they recommend turning off Javascript.
Open up Adobe Reader/Acrobat and turn off JavaScript! Yes, PDFs can have Javascript, though you've probably never even seen a PDF file that legitimately uses Javascript.
Here is how you do it in Reader 9.1.x :
Click on the Edit menu, click Preferences.
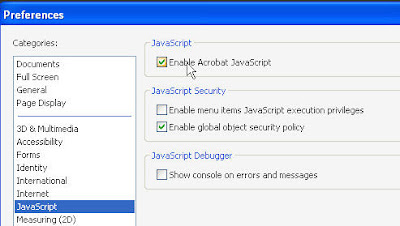 Select Javascript from the Categories menu.
Select Javascript from the Categories menu.Click the checkbox OFF next to Enable Acrobat JavaScript
Saturday, October 03, 2009
Loading CD-ROMs On A Netbook
Most people know you can get a USB CD-ROM drive and fix that.
A few know about CD-ROM emulators like the one included with Alcohol 120%... but that has an extra cost.
After a little browsing around the net I found a FREE CD-ROM emulator from Microsoft!
Download the Microsoft Virtual CD-ROM Control Panel package now.
Thursday, October 01, 2009
OWASP top 10
OWASP Top 10 Security Vulnerabilities Part 1 (Barry Dorrans) from Edge UG on Vimeo.
OWASP Top 10 Security Vulnerabilities Part 2 (Barry Dorrans) from Edge UG on Vimeo.
Friday, September 04, 2009
Gmail Security
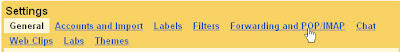
 First, log in and then click the Settings tab as shown.
First, log in and then click the Settings tab as shown.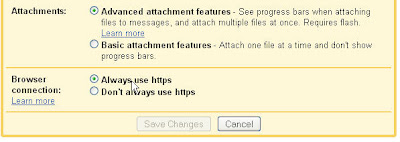 Now scroll down to the bottom and check the "Always use https" option.
Now scroll down to the bottom and check the "Always use https" option.This will help keep people from spying on you at public WiFi stations like McDonalds, Starbucks, or the library.
 Now for the more convenient part...
Now for the more convenient part...You can actually check Gmail in your own e-mail program! You don't need to log into the website, or to download some special Gmail only software to get the "you have mail" pop-up.
Click on the "Forwarding and POP/IMAP" link.
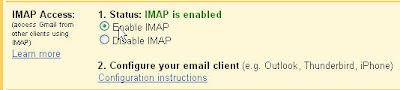 Down at the bottom, again you will find the "Enable IMAP" option. Turn that on.
Down at the bottom, again you will find the "Enable IMAP" option. Turn that on.Then follow the instructions in the Configuration instructions shown as step 2 in the image.
make sure you always select SSL as the connection method. (on port 993)
DO NOT cheat and select the gmail option in Thunderbird if that is your mail client. That will set you up with unencrypted POP mail. Trust me you want SSL encrypted IMAP. In fact, no matter who you are getting your e-mail from, you want SSL, or better yet, TLS encrypted IMAP. POP is so 1994. (and if you run it unencrypted you are enabling "Big Brother"...so maybe I should have said it's so 1984.)
PCI DSS
 Click for a free PDF copy
Click for a free PDF copyThe Payment Card Industry (PCI) Data Security Standard (DSS) is something you have already agreed to, and MUST follow. Does your bill for your merchant account include a line about non-compliance fees? This is what it's about.
GFI LanGuard

There are all kinds of different network vulnerability scanners out there, but the best bet for small businesses is probably GFI Languard.
The reason? It's simple and it's free.
It is an easy to use Windows based program, so no need to learn or install Linux to use it.
It is absolutely free if you have 5 or fewer IP addresses (computers) to scan.
It is free for a 30day trial if you have more than 5 IPs to scan.
Wednesday, September 02, 2009
VirusTotal
If you get an e-mail attachment that you really are not sure about, and your own AV doesn't see a problem, you can check it here and know with some certainty that at least no other AV vendor sees the problem.
Monday, August 31, 2009
Secunia - Keep ALL Your Software Up To Date
But what about all the other programs you run? do you know you are upto date?
Secunia will tell you.
You can go to their web portal for a free scan of your system any time you like, and it will check it all for you. If you are using it at home you can download Secunia PSI (Personal Software Inspector) or if it is for business use there is the cooler sounding Secunia CSI (Corporate...) at a cost, but well worth it.
Wednesday, August 26, 2009
SecTor 2009 - Last week for discount pricing

SecTor (Toronto's big InfoSec conference) admission prices go up on Sept 1.
If you haven't got your tickets yet now is the time.
After Sept. 1 it'll cost $250 more to get in to this great IT security conference.
If you are a member of TASK or OWASP You can get an additional 10% off, just look through those mailing lists, there have been discount codes posted.
There are some great speakers booked for this year. I'm really looking forward to it.
Tuesday, August 11, 2009
Canadian pricing for Windows 7 family pack
Read more at Digital Home.
Thursday, June 25, 2009
Monday, June 15, 2009
Wednesday, June 10, 2009
BlackBerries and E-Mail
Yes I can access my IMAP account from my Blackberry, but it has to use an intermediary server hosted by RIM which means that I have to enter my e-mail credentials for my private personal account into RIM's server so that it can check my IMAP mail and relay it to my Blackberry. Why doesn't my Blackberry come with an IMAP capable e-mail client?
The way they are doing it now has several problems.
#1 I have to give RIM my account info instead of just inputting it into a device that would normally be on my person.
#2 I can't access anything but the inbox. None of the other folders are available via this 2 stage e-mail retrieval process.
#3 (ok this is more a complaint about the OTHER type of e-mail BlackBerries do....) My BES e-mail from work doesn't get it's own icon like the BIS ones do so while I can look at each of my personal mail accounts individually, when I want to read my work e-mails it's all mixed up with the e-mails from my home accounts.
If I could have encrypted IMAP done on a 400 Mhz ARM processor 8 years ago, why can't my BB Storm do it?
Friday, May 22, 2009
Why isn't Apple giving us a patch?
SANS Internet Storm Center doesn't know either.
http://isc.sans.org/diary.html?storyid=6442&rss
Wednesday, May 20, 2009
Klingons need antivirus too.
You think you're immune just because you run MacOS or Linux, but not even the Klingons can keep today's malware at bay without a little help.
Wednesday, April 29, 2009
SecTor 2009 - Early bird registration ends tomorrow
SecTor (short for Secure Toronto, I believe) is a conference for Information Security folks in Toronto, Ontario, Canada.
It is Oct. 6 & 7 this year, with training courses on the 5th for those who desire a bit of heavy duty security training before the conference. The training on the 5th is in any one of these topics:
| Session Title | Presenter | Cost | Link |
| Securing your Microsoft Infrastructure | Brian Bourne CMS Consutlting Inc. | $999 | Register |
| Understanding Web Application Attacks | Security Compass | $999 | Register |
| Auditing systems and networks with Backtrack 4 | The Academy | $999 | Register |
| Data Forensics – Essentials for Survival | Robb Beggs, Digital Defence Larry Gagnon, Forensicom | $999 | Register |
Currently you can get admission to the 2 day conference for only $499 After May 1st it goes up to $749. ...and for the really tardy, tickets will be available at $999 after Sept. 1st. (if there are still tickets to be had)
(Hint: TASK [Toronto Area Security Klatch] has a 10% off coupon to reduce that price even further, but I 'm not going to tell you what it is, if you really want it you can find out for yourself.)
SecTor 2009 Tickets are Limited!
CLICK HERE TO REGISTER NOW
Sunday, April 26, 2009
Big news for fans of Windows.
Basically, any owner of a copy of Windows 7 Professional, Enterprise or Ultimate (which covers just about everyone who will be using it in a corporate environment, and a lot of home users). will be entitled to download what is essentially a copy of Windows XP in a virtual machine that will run in parallel with Windows 7, seamlessly integrating it's windows and icons with the host Windows 7 ones, thereby relieving Microsoft of the need to keep old code in Windows 7 and future versions for compatiblity with old software. If it won't run in windows 7 you install it as an XP compatibility install and it runs in XP on top of Windows 7.
Tuesday, April 14, 2009
Microsoft prepping IE8 auto update
IE8 will be available to WSUS in July 2009.
Visit the Microsoft IE blog for more info.
Sunday, April 12, 2009
Twitter hit by a worm on Saturday
A worm infected Twitter on Saturday April 11, 2009.
The worm seems to have originated at the StalkDaily.com site, as it seems that it's main purpose is to direct people there. Twitter warned people against visiting the site or linking to it.
The worm sends spam tweets from the infected person's account that direct others to the StalkDaily site. Simply visiting the profile page of an infected user can lead to one's own profile getting infected.
If you have been locked out of your twitter account due to this worm, you need to do a password reset as Twitter has locked some infected accounts.
Twitter claims to have now fixed the security hole that enabled this worm, and that no passwords, phone numbers, or other sensitive information were compromised as part of this attack.
Saturday, March 28, 2009
Ubuntu 9.04 Beta ... and cloud computing
I don't recommend the beta release for anything you want to keep working and stable, but if you want to run the liveCD and get a preview of what's coming at the end of April it's here.
9.04 promises faster boot up and support for the new Linux file system ext4. It also provides the really ambitious folks the tools to build a cloud computing server system.
This may be an interesting year for Linux. Cloud computing is hot and with all the little mini laptops on the market (perfect clients for cloud computing clusters) I imagine it'll get hotter. Ubuntu is packaging the tools for the server guys to use into it's system... It's only a matter of time I think before cloud services start popping up in large numbers.
Thursday, March 19, 2009
Internet Explorer 8
The most touted feature seems to be InPrivate Browsing, which lets you browse the web without saving your history. A number of other new features are added in IE8 though, so check it out. IE 8 is also supposed to be better at identifying and blocking malware sites. That alone is worth the download.
Tuesday, March 10, 2009
Need to Budget?
Thursday, February 26, 2009
Improving Your Mac's Firewall
it is very limited in it's capabilities.
NoobProof and WaterRoof are both free (open source) firewall front-ends from hanynet.com that improve the flexibility of the Mac's built-in IPFW firewall.
WaterRoof is a very complex and powerful tool, which allows you to configure almost every aspect and option of "ipfw". And more, you can list/manage active connections or network files, do graphics log analisys, configure your mac as a router with bandwidth management with stateful rules and tons of other options. You need a good knowledge of "what a firewall is", and you should also have at least a basic ipfw knowledge.
NoobProof is a very easy tool. When you start it the first time you have a service list and you can choose to "allow" or "deny" connections to those services. So you have only to decide which service to allow, and then check "Activate NoobProof". You can also add selective "allow" and "deny", and you can delete or add new custom services in service list.
| COMPARISON TABLE | WaterRoof | NoobProof |
| Static rules list | x | x |
| Customizable dynamic service list | x | |
| Customizable rules builder | x | |
| Startup Script and Startup configuration | x | x |
| Import and export firewall configuration | x | |
| Bandwidth Management (Dummynet) | x | |
| NAT setup (Network Address Translation) | x | |
| Dynamic rules (stateful firewall) | x | |
| Ready rule sets | x | |
| Logs listing | x | x |
| Logs parsing and graphic statistics | x | |
| Network connections and applications list | x | |
| Network connections selective block or limit | x | |
| Appfirewall debug and logs listing | x | |
| Interface list and DNS/WHOIS queries | x | |
| Configuration Wizard | x |
Wednesday, February 25, 2009
Windows 7...It's better than Vista. Promise.
Trust me, from what I've seen it is better than Vista.
http://i.i.com.com/cnwk.1d/i/tr/downloads/home/dl_10_vista_haters.pdf
Tuesday, February 24, 2009
Tuesday, January 27, 2009
IE8 RC1 released today
You can get it here: http://www.microsoft.com/windows/internet-explorer/beta/
This follow up to previous versions of IE that I'm sure everyone is familiar with adds private browsing (with no history recorded for private sessions) and improved security features.
It also allows you to simulate earlier versions for websites that insist on a specific version.
And while you are at it, if you have a spare machine just laying around, or if you are geeky enough to use a virtual machine (like me) download Windows 7 beta too.
http://www.microsoft.com/windows/windows-7/beta-download.aspx
It's like an improved, faster Vista. But make sure you have the minimum system requirements and that you have no problem with the computer just stopping when the Windows beta expires on Aug 1.
Saturday, January 24, 2009
Mac trojan - Beware of pirate iLife 09
Thursday, January 15, 2009
NOT the end of Nortel
They have only applied for creditor protection. They are not closing shop, just re-organizing.
The new Nortel may be a slimmer Nortel after this, but I strongly believe that we will still have Nortel around for many years to come.
They say they will still be doing R&D. As much as they have been? Who knows? Time will tell.
They will still sell products. Will they eliminate some products? Will they sell off some lines of products to other companies just as they bought up product lines like Bay Networks switches? Maybe.
The CEO released a statement and video here: http://www.nortel.com/corporate/restructuring.html
...and they have an investor's FAQ here: http://www.nortel.com/corporate/collateral/investor_faq.pdf



